Standard binary encryption is insufficient for image data due to high spatial correlation between neighboring pixels (e.g., gradients, uniform color regions). A dedicated image cipher must destroy these statistical fingerprints. The authors propose a three-stage pipeline leveraging hyperchaotic systems—deterministic systems with sensitivity to initial conditions and divergence along multiple independent dimensions—to generate high-entropy keystreams and dynamic substitution boxes (S-boxes).
Here’s a simple kitchen analogy to explain the concept, mechanism, and tradeoff of the FPGA-based hyperchaos image encryption algorithm from that paper.
Alexan, Wassim, Elshabasy, Noura H., Mamdouh, Eyad, Osama, Remas, Abd El Ghany, Mohamed A., El-Damak, Dina, FPGA Realization of a Novel Hyperchaos Augmented Image Encryption Algorithm, IET Computers & Digital Techniques, 2026, 6416727, 32 pages, 2026. https://doi.org/10.1049/cdt2/6416727
The Analogy: Making an Unrecognizable, Secret Smoothie
Say, you have a photo of a sliced fruit platter. You want to hide it completely so no one can guess what fruits were there.
A simple method might just shuffle the slices – but someone could still see “lots of red = strawberries.”
Instead, you want to destroy all patterns – turn it into a smoothie so uniform that you can’t tell what went in.
The encryption pipeline consists of three sequential stages, each using a hyperchaotic system of increasing dimensionality (6D → 8D → 9D):
1. Keystream Generation: Each stage numerically solves its hyperchaotic system using given initial conditions to produce a pseudo-random bitstream.
2. XOR Diffusion: The flattened image bitstream is XORed with the keystream to obscure spatial structure.
3. Dynamic S-Box Substitution: A byte-level lookup table is generated from the chaotic trajectory, mapping each input byte to a permuted output byte. This breaks the relationship between key and ciphertext (confusion).
4. Cascading: Output of stage 1 feeds into stage 2, then stage 3. Each successive layer adds higher-dimensional randomness, forcing an attacker to break three independent chaotic transforms.
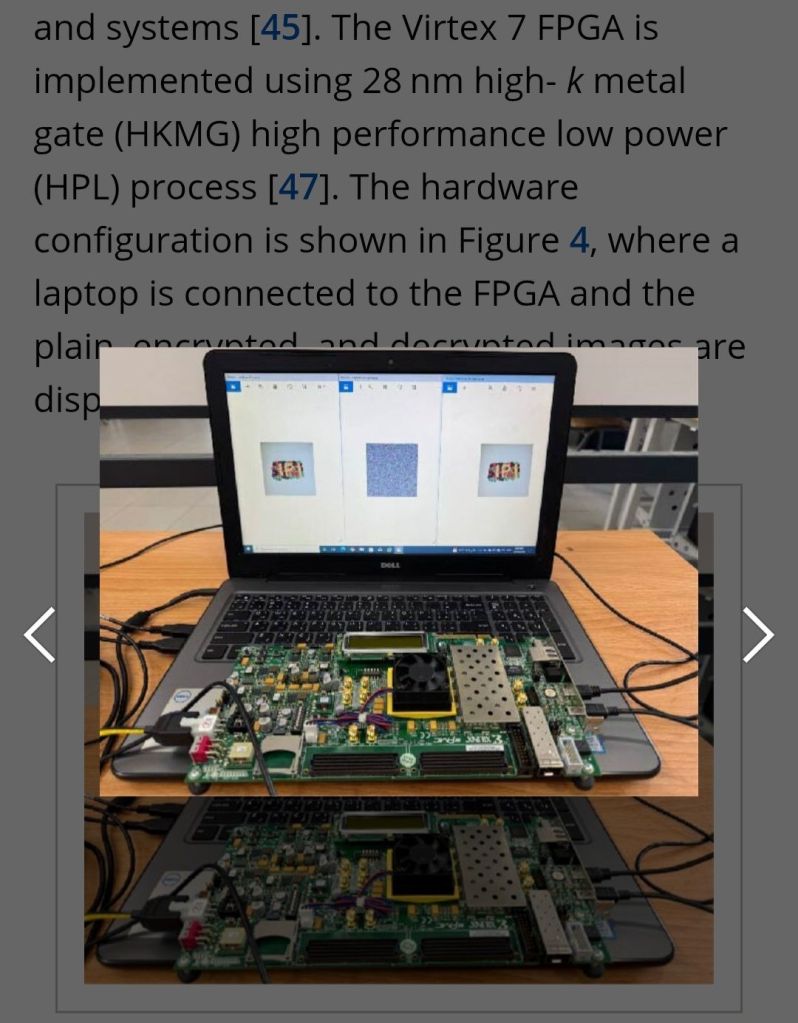
FPGA Implementation
The algorithm is implemented on a Field-Programmable Gate Array (FPGA), configured as a streaming pipeline:
· Each encryption stage maps directly to a dedicated hardware datapath.
· Operations run in parallel with minimal buffering and bounded latency.
· Unlike GPUs, FPGAs avoid host-device memory transfers and scheduler overhead, offering deterministic, low-latency, energy-efficient processing.
How it works, step by step
- Stage 1 – Chaotic blender (6D)
You toss the fruit into a blender whose speed changes in a very sensitive, unpredictable way (hyperchaos).
· It first XORs = roughly, “purees” the fruit with a random-looking pattern.
· Then it passes through an S-box = a secret lookup table that swaps each fruit piece for a totally different “fake fruit” according to a rule that changes with the blender’s settings. - Stage 2 – Second blender (8D)
You take that puree and run it through a more complex blender (more dimensions of chaos). It again mixes and substitutes, but with an even richer set of movements. - Stage 3 – Final blender (9D)
One last pass with the most complex blender. By now, the original fruit is mathematically unrecognizable. - FPGA = A custom kitchen robot
Instead of a human chef using one spoon (a normal CPU), you build a dedicated assembly line in hardware. Three blenders sit in a row; fruit goes in one side, encrypted smoothie comes out the other side continuously – all stages running at the same time.
What you gain vs. what you lose
Gain Loss / Cost
✅ Extremely strong encryption – breaks all statistical patterns in images
❌ Much harder to design than a simple algorithm (3 complex chaos systems)
✅ Fast and low latency – FPGA does all stages in parallel, like an assembly line
❌ Inflexible – you can’t easily change the recipe (unlike software)
✅ Resists future attacks – even if one chaos layer is cracked, two more remain
❌ Uses specialized hardware (FPGA), not something you run on a normal laptop
✅ Low power for high throughput
❌ Long development time – programming FPGAs is like wiring a circuit, not writing a script
This method is like pureeing fruit through three increasingly chaotic blenders on a custom kitchen assembly line – incredibly secure and fast, but only worth it if you need industrial-grade protection and can build the special hardware.
Leave a comment